Generate Public And Private Key For Jwt
Posted : admin On 20.04.2020Create JSON Web Tokens signed with your private key to authorize API requests.
To install the public key, Log into the server, edit the authorizedkeys file with your favorite editor, and cut-and-paste the public key output by the above command to the authorizedkeys file. Save the file. Configure PuTTY to use your private key file (here keyfile.ppk). Then test if login works. See configuring public key authentication for. Jun 11, 2018 In this article I'm going to show you how to generate JWTs that can be verified without having access to the signing secret key. For more information, read my blog post: https://blog. Use the private key associated with the key ID you specified in the header to sign the token. Regardless of the programming language you're using with the App Store Connect API, there are a variety of open source libraries available online for creating and signing JWT tokens.
Sep 09, 2017 A little NodeJS demo of making and verifing JavaScript Web Tokens (JWT) using RSA Public/Private Key Pairs Table of Contents: 00:00 - Introduction 00:44 - 1. Get a RSA public/private PEM pair 01. I want to use the JWT with the RS256 algorithm using implementation in the.NET. I've used the library System.IdentityModel.Tokens.Jwt. This library supports the RS256 algorithm. How can I generate the private and public certificates on Windows?
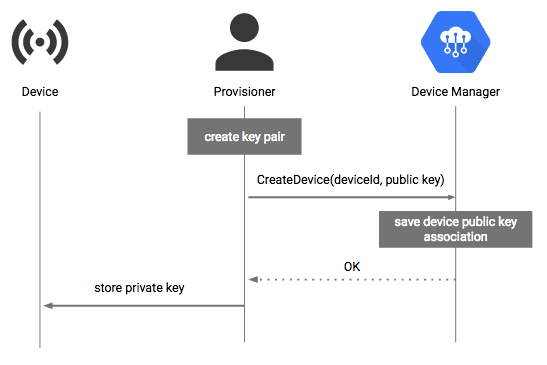
Overview
JSON Web Token (JWT) is an open standard (RFC 7519) that defines a way to securely transmit information. The App Store Connect API requires JWTs to authorize each API request. You create the token, signing it with the private key you downloaded from App Store Connect.
To generate a signed JWT:
Create the JWT header.
Create the JWT payload.
Sign the JWT.
Include the signed JWT in the authorization header of each App Store Connect API request.
Create the JWT Header
To create a JWT to communicate with the App Store Connect API, use the following fields and values in the header:
To get your key ID, copy it from App Store Connect by logging in to App Store Connect, then:
Select Users and Access, then select the API Keys tab.
The key IDs appear in a column under the Active heading. Hover the cursor next to a key ID to display the Copy Key ID link.
Click Copy Key ID.
If you have more than one API key, use the key ID of the same private key that you use to sign the JWT.
Here's an example of a JWT header:
Create the JWT Payload
The JWT payload contains information specific to the App Store Connect APIs, such as issuer ID and expiration time. Use the following fields and values in the JWT payload:
To get your issuer ID, log in to App Store Connect and:
Select Users and Access, then Select the API Keys tab.
The issuer ID appears near the top of the page. To copy the issuer ID, click Copy next to the ID.
Here's an example of a JWT payload:
Sign the JWT
Use the private key associated with the key ID you specified in the header to sign the token.
Regardless of the programming language you're using with the App Store Connect API, there are a variety of open source libraries available online for creating and signing JWT tokens. See JWT.io for more information.
Tip
You do not need to generate a new token for every API request. To get better performance from the App Store Connect API, reuse the same signed token for up to 20 minutes.
Include the JWT in the Request's Authorization Header
Jwt Private Key
Once you have a complete and signed token, provide the token in the request's authorization header as a bearer token.
The following example shows a curl command using a bearer token. Replace the text '[signed token]' with the value of the signed token itself.
See Also
Creating API Keys for App Store Connect APICreate API keys used to sign JWTs and authorize API requests.
Hi.I notice that the test file use readPublicKeyFromFile and readPublicKeyFromFile use parsePEMFile,but there is no doc about the parsePEMFile.
The parsePEMFile method use PemReader to read the key from file,but the question is at the first time there is no file such as src/test/resources/rsa-public.pem.I check the the src code,but I don't understand why throw a error rather than create the key pair and create the file and put the key pair into it.
So I don't know how the getPublicKey method generate the public and private key.
According to current java-jwt api,we must create the public and privte key files before we use the api,it's a little inconvenient.
On the other hand,I don't use jsp or spring or spring mvc.I just use struts2 for the json api.
Screen connect mfa key generator. Enable Multi-Factor Authentication on your IT Glue account. Login as ITGlue admin. Go to account tab. Select Users tab on left hand side. Select the pencil next to username to edit the user account. Under Multi-Factor Authentication Settings, Enabled Multi-Factor Authentication.
Jwt Generate Key
Final question,when we create the token,we use JWT.create().withIssuedAt(date) and here the date is type of Date,but I find that when we vertify the token,the verifyClaims method convert Date to Long?I test (Long)(new Date()),it will throw error,but the verifyClaims method won't,so I want to how it works?
Could any one help me?.Thanks a lot.