Generate 256 Bit Key Python
Posted : admin On 15.04.2020Oct 05, 2016 Generate truly random cryptographic keys using a random number generator in.NET. The RNGCryptoServiceProvider class will generate random bytes in a fixed-length byte array. Cryptographic algorithms require keys of specific length such as 32-bit or 256-bit keys. Ssh uses asymmetric keys in order to encrypt and made traffic invisible to the others those resides between systems in the network. The encryption power comes from key bit size or length. In this tutorial we will look how to create 4096 bit keys. Generate 4098 Bit Key. In this example we will generate very secure key. Jul 16, 2018 In Python, there are at least two classes that can keep the private and public keys: “str” and “bytes”. The first is a string and the second is a byte array. Cryptographic methods in Python work with a “bytes” class, taking it as input and returning it as the result.
Source code:Lib/hashlib.py
This module implements a common interface to many different secure hash andmessage digest algorithms. Included are the FIPS secure hash algorithms SHA1,SHA224, SHA256, SHA384, and SHA512 (defined in FIPS 180-2) as well as RSA’s MD5algorithm (defined in Internet RFC 1321). The terms “secure hash” and“message digest” are interchangeable. Older algorithms were called messagedigests. The modern term is secure hash.
Note
If you want the adler32 or crc32 hash functions, they are available inthe zlib module.
Warning
Some algorithms have known hash collision weaknesses, refer to the “Seealso” section at the end.
Hash algorithms¶
There is one constructor method named for each type of hash. All returna hash object with the same simple interface. For example: use sha256() tocreate a SHA-256 hash object. You can now feed this object with bytes-likeobjects (normally bytes) using the update() method.At any point you can ask it for the digest of theconcatenation of the data fed to it so far using the digest() orhexdigest() methods.
Note
For better multithreading performance, the Python GIL is released fordata larger than 2047 bytes at object creation or on update.
Note
Feeding string objects into update() is not supported, as hashes workon bytes, not on characters.
Constructors for hash algorithms that are always present in this module aresha1(), sha224(), sha256(), sha384(),sha512(), blake2b(), and blake2s().md5() is normally available as well, though itmay be missing if you are using a rare “FIPS compliant” build of Python.Additional algorithms may also be available depending upon the OpenSSLlibrary that Python uses on your platform. On most platforms thesha3_224(), sha3_256(), sha3_384(), sha3_512(),shake_128(), shake_256() are also available.
New in version 3.6: SHA3 (Keccak) and SHAKE constructors sha3_224(), sha3_256(),sha3_384(), sha3_512(), shake_128(), shake_256().
New in version 3.6: blake2b() and blake2s() were added.
For example, to obtain the digest of the byte string b'Nobodyinspectsthespammishrepetition':
More condensed:
hashlib.new(name[, data])¶Is a generic constructor that takes the string name of the desiredalgorithm as its first parameter. It also exists to allow access to theabove listed hashes as well as any other algorithms that your OpenSSLlibrary may offer. The named constructors are much faster than new()and should be preferred.
Using new() with an algorithm provided by OpenSSL:
Hashlib provides the following constant attributes:
hashlib.algorithms_guaranteed¶A set containing the names of the hash algorithms guaranteed to be supportedby this module on all platforms. Note that ‘md5’ is in this list despitesome upstream vendors offering an odd “FIPS compliant” Python build thatexcludes it.
New in version 3.2.
hashlib.algorithms_available¶A set containing the names of the hash algorithms that are available in therunning Python interpreter. These names will be recognized when passed tonew(). algorithms_guaranteed will always be a subset. Thesame algorithm may appear multiple times in this set under different names(thanks to OpenSSL).
The following values are provided as constant attributes of the hash objectsreturned by the constructors:
hash.digest_size¶The size of the resulting hash in bytes.
hash.block_size¶The internal block size of the hash algorithm in bytes.
A hash object has the following attributes:
hash.name¶The canonical name of this hash, always lowercase and always suitable as aparameter to new() to create another hash of this type.
Changed in version 3.4: The name attribute has been present in CPython since its inception, butuntil Python 3.4 was not formally specified, so may not exist on someplatforms.
A hash object has the following methods:
hash.update(data)¶Update the hash object with the bytes-like object.Repeated calls are equivalent to a single call with theconcatenation of all the arguments: m.update(a);m.update(b) isequivalent to m.update(a+b).
Changed in version 3.1: The Python GIL is released to allow other threads to run while hashupdates on data larger than 2047 bytes is taking place when using hashalgorithms supplied by OpenSSL.
hash.digest()¶Return the digest of the data passed to the update() method so far.This is a bytes object of size digest_size which may contain bytes inthe whole range from 0 to 255.
hash.hexdigest()¶Like digest() except the digest is returned as a string object ofdouble length, containing only hexadecimal digits. This may be used toexchange the value safely in email or other non-binary environments.
hash.copy()¶Return a copy (“clone”) of the hash object. This can be used to efficientlycompute the digests of data sharing a common initial substring.
SHAKE variable length digests¶
The shake_128() and shake_256() algorithms provide variablelength digests with length_in_bits//2 up to 128 or 256 bits of security.As such, their digest methods require a length. Maximum length is not limitedby the SHAKE algorithm.
shake.digest(length)¶Return the digest of the data passed to the update() method so far.This is a bytes object of size length which may contain bytes inthe whole range from 0 to 255.
shake.hexdigest(length)¶Like digest() except the digest is returned as a string object ofdouble length, containing only hexadecimal digits. This may be used toexchange the value safely in email or other non-binary environments.
Remote Desktop Protocol (RDP) is a protocol developed by Microsoft. It is used to control and manage machines with a Windows operating system remotely.Unlike Secure Shell, connections established using an RDP client provide a user with a graphical interface through which they can gain access to a remote computer and control it in the same manner as their local computer.Using Remote Desktop services, formerly known as terminal services, allows network and system engineers to easily manipulate remote computers connected to a local network or the Internet.This comes with a price. An example of an IP address would be 172.16.0.5 and the example of a hostname would be myserver.somedomain.com. Copy ssh key linux.
Key derivation¶
Key derivation and key stretching algorithms are designed for secure passwordhashing. Naive algorithms such as sha1(password) are not resistant againstbrute-force attacks. A good password hashing function must be tunable, slow, andinclude a salt.
hashlib.pbkdf2_hmac(hash_name, password, salt, iterations, dklen=None)¶The function provides PKCS#5 password-based key derivation function 2. Ituses HMAC as pseudorandom function.
The string hash_name is the desired name of the hash digest algorithm forHMAC, e.g. ‘sha1’ or ‘sha256’. password and salt are interpreted asbuffers of bytes. Applications and libraries should limit password toa sensible length (e.g. 1024). salt should be about 16 or more bytes froma proper source, e.g. os.urandom().
The number of iterations should be chosen based on the hash algorithm andcomputing power. As of 2013, at least 100,000 iterations of SHA-256 aresuggested.
dklen is the length of the derived key. If dklen is None then thedigest size of the hash algorithm hash_name is used, e.g. 64 for SHA-512.
New in version 3.4.
Note
A fast implementation of pbkdf2_hmac is available with OpenSSL. ThePython implementation uses an inline version of hmac. It is aboutthree times slower and doesn’t release the GIL.
hashlib.scrypt(password, *, salt, n, r, p, maxmem=0, dklen=64)¶The function provides scrypt password-based key derivation function asdefined in RFC 7914.
password and salt must be bytes-like objects. Applications and libraries should limit passwordto a sensible length (e.g. 1024). salt should be about 16 or morebytes from a proper source, e.g. os.urandom().
n is the CPU/Memory cost factor, r the block size, p parallelizationfactor and maxmem limits memory (OpenSSL 1.1.0 defaults to 32 MiB).dklen is the length of the derived key.
Availability: OpenSSL 1.1+.
BLAKE2¶
BLAKE2 is a cryptographic hash function defined in RFC 7693 that comes in twoflavors:
BLAKE2b, optimized for 64-bit platforms and produces digests of any sizebetween 1 and 64 bytes,
BLAKE2s, optimized for 8- to 32-bit platforms and produces digests of anysize between 1 and 32 bytes.
BLAKE2 supports keyed mode (a faster and simpler replacement for HMAC),salted hashing, personalization, and tree hashing.
Hash objects from this module follow the API of standard library’shashlib objects.
Creating hash objects¶
New hash objects are created by calling constructor functions:
hashlib.blake2b(data=b', *, digest_size=64, key=b', salt=b', person=b', fanout=1, depth=1, leaf_size=0, node_offset=0, node_depth=0, inner_size=0, last_node=False)¶
hashlib.blake2s(data=b', *, digest_size=32, key=b', salt=b', person=b', fanout=1, depth=1, leaf_size=0, node_offset=0, node_depth=0, inner_size=0, last_node=False)¶
These functions return the corresponding hash objects for calculatingBLAKE2b or BLAKE2s. They optionally take these general parameters:
data: initial chunk of data to hash, which must bebytes-like object. It can be passed only as positional argument.
digest_size: size of output digest in bytes.
key: key for keyed hashing (up to 64 bytes for BLAKE2b, up to 32 bytes forBLAKE2s).
salt: salt for randomized hashing (up to 16 bytes for BLAKE2b, up to 8bytes for BLAKE2s).
person: personalization string (up to 16 bytes for BLAKE2b, up to 8 bytesfor BLAKE2s).
The following table shows limits for general parameters (in bytes):
Hash | digest_size | len(key) | len(salt) | len(person) |
|---|---|---|---|---|
BLAKE2b | 64 | 64 | 16 | 16 |
BLAKE2s | 32 | 32 | 8 | 8 |
Note
BLAKE2 specification defines constant lengths for salt and personalizationparameters, however, for convenience, this implementation accepts bytestrings of any size up to the specified length. If the length of theparameter is less than specified, it is padded with zeros, thus, forexample, b'salt' and b'saltx00' is the same value. (This is notthe case for key.)
These sizes are available as module constants described below.
Constructor functions also accept the following tree hashing parameters:
fanout: fanout (0 to 255, 0 if unlimited, 1 in sequential mode).
depth: maximal depth of tree (1 to 255, 255 if unlimited, 1 insequential mode).
leaf_size: maximal byte length of leaf (0 to 2**32-1, 0 if unlimited or insequential mode).
node_offset: node offset (0 to 2**64-1 for BLAKE2b, 0 to 2**48-1 forBLAKE2s, 0 for the first, leftmost, leaf, or in sequential mode).
node_depth: node depth (0 to 255, 0 for leaves, or in sequential mode).
inner_size: inner digest size (0 to 64 for BLAKE2b, 0 to 32 forBLAKE2s, 0 in sequential mode).
last_node: boolean indicating whether the processed node is the lastone (False for sequential mode).
See section 2.10 in BLAKE2 specification for comprehensive review of treehashing.
Constants¶
blake2b.SALT_SIZE¶
blake2s.SALT_SIZE¶
Salt length (maximum length accepted by constructors).
blake2b.PERSON_SIZE¶
blake2s.PERSON_SIZE¶
Personalization string length (maximum length accepted by constructors).
blake2b.MAX_KEY_SIZE¶
blake2s.MAX_KEY_SIZE¶
Maximum key size.
blake2b.MAX_DIGEST_SIZE¶
blake2s.MAX_DIGEST_SIZE¶
Maximum digest size that the hash function can output.
Examples¶
Simple hashing¶
To calculate hash of some data, you should first construct a hash object bycalling the appropriate constructor function (blake2b() orblake2s()), then update it with the data by calling update() on theobject, and, finally, get the digest out of the object by callingdigest() (or hexdigest() for hex-encoded string).
As a shortcut, you can pass the first chunk of data to update directly to theconstructor as the positional argument:
You can call hash.update() as many times as you need to iterativelyupdate the hash:
Using different digest sizes¶
BLAKE2 has configurable size of digests up to 64 bytes for BLAKE2b and up to 32bytes for BLAKE2s. For example, to replace SHA-1 with BLAKE2b without changingthe size of output, we can tell BLAKE2b to produce 20-byte digests:
Hash objects with different digest sizes have completely different outputs(shorter hashes are not prefixes of longer hashes); BLAKE2b and BLAKE2sproduce different outputs even if the output length is the same:
Keyed hashing¶
Keyed hashing can be used for authentication as a faster and simplerreplacement for Hash-based message authentication code (HMAC).BLAKE2 can be securely used in prefix-MAC mode thanks to theindifferentiability property inherited from BLAKE.
This example shows how to get a (hex-encoded) 128-bit authentication code formessage b'messagedata' with key b'pseudorandomkey':
As a practical example, a web application can symmetrically sign cookies sentto users and later verify them to make sure they weren’t tampered with:
Even though there’s a native keyed hashing mode, BLAKE2 can, of course, be usedin HMAC construction with hmac module:
Randomized hashing¶
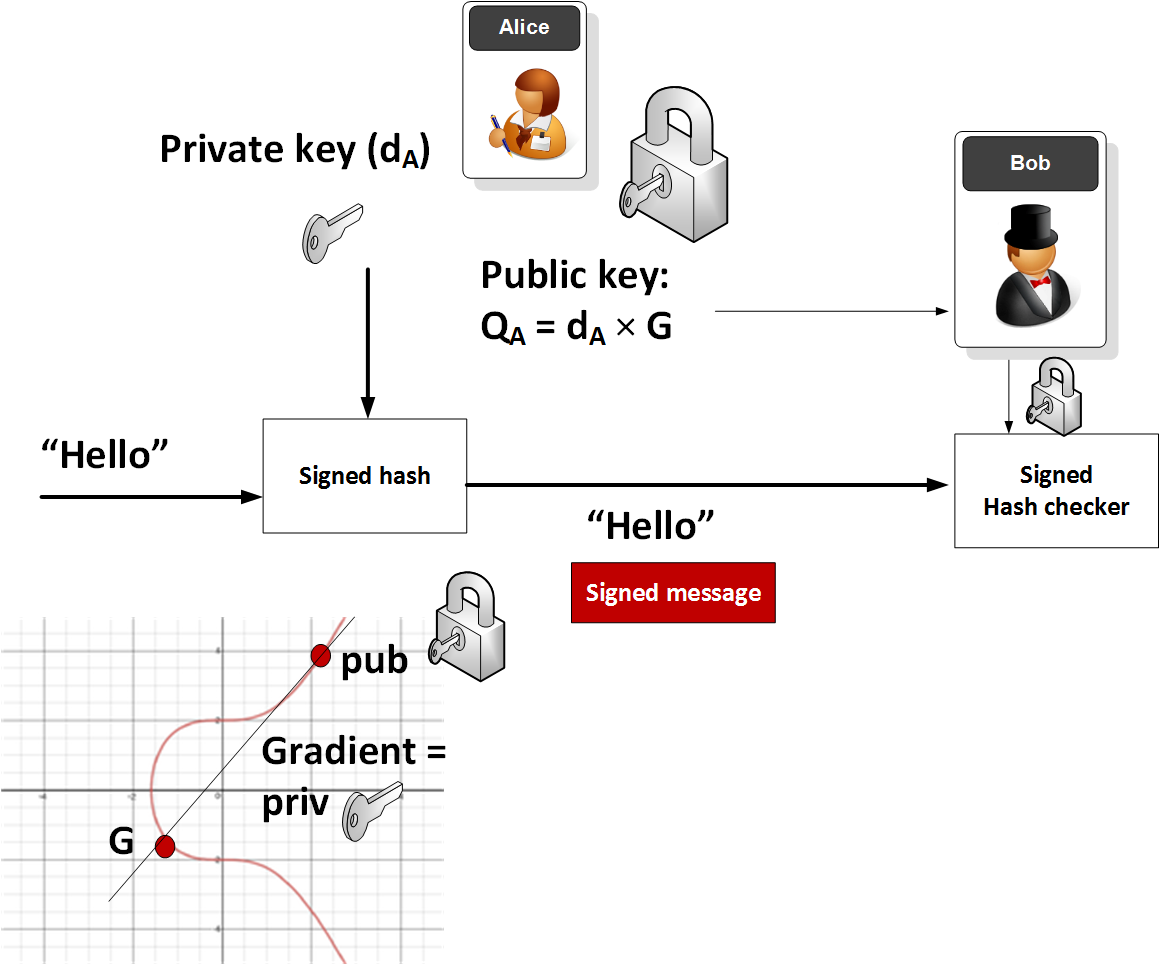
By setting salt parameter users can introduce randomization to the hashfunction. Randomized hashing is useful for protecting against collision attackson the hash function used in digital signatures.
Randomized hashing is designed for situations where one party, the messagepreparer, generates all or part of a message to be signed by a secondparty, the message signer. If the message preparer is able to findcryptographic hash function collisions (i.e., two messages producing thesame hash value), then they might prepare meaningful versions of the messagethat would produce the same hash value and digital signature, but withdifferent results (e.g., transferring $1,000,000 to an account, rather than$10). Cryptographic hash functions have been designed with collisionresistance as a major goal, but the current concentration on attackingcryptographic hash functions may result in a given cryptographic hashfunction providing less collision resistance than expected. Randomizedhashing offers the signer additional protection by reducing the likelihoodthat a preparer can generate two or more messages that ultimately yield thesame hash value during the digital signature generation process — even ifit is practical to find collisions for the hash function. However, the useof randomized hashing may reduce the amount of security provided by adigital signature when all portions of the message are preparedby the signer.
(NIST SP-800-106 “Randomized Hashing for Digital Signatures”)
In BLAKE2 the salt is processed as a one-time input to the hash function duringinitialization, rather than as an input to each compression function.
Warning
Salted hashing (or just hashing) with BLAKE2 or any other general-purposecryptographic hash function, such as SHA-256, is not suitable for hashingpasswords. See BLAKE2 FAQ for moreinformation.
Personalization¶
Sometimes it is useful to force hash function to produce different digests forthe same input for different purposes. Quoting the authors of the Skein hashfunction:
We recommend that all application designers seriously consider doing this;we have seen many protocols where a hash that is computed in one part ofthe protocol can be used in an entirely different part because two hashcomputations were done on similar or related data, and the attacker canforce the application to make the hash inputs the same. Personalizing eachhash function used in the protocol summarily stops this type of attack.
(The Skein Hash Function Family,p. 21)
BLAKE2 can be personalized by passing bytes to the person argument:
Personalization together with the keyed mode can also be used to derive differentkeys from a single one.
Tree mode¶
Here’s an example of hashing a minimal tree with two leaf nodes:
This example uses 64-byte internal digests, and returns the 32-byte finaldigest:
Credits¶
BLAKE2 was designed by Jean-Philippe Aumasson, Samuel Neves, ZookoWilcox-O’Hearn, and Christian Winnerlein based on SHA-3 finalist BLAKEcreated by Jean-Philippe Aumasson, Luca Henzen, Willi Meier, andRaphael C.-W. Phan.
It uses core algorithm from ChaCha cipher designed by Daniel J. Bernstein.
The stdlib implementation is based on pyblake2 module. It was written byDmitry Chestnykh based on C implementation written by Samuel Neves. Thedocumentation was copied from pyblake2 and written by Dmitry Chestnykh.
The C code was partly rewritten for Python by Christian Heimes.
The following public domain dedication applies for both C hash functionimplementation, extension code, and this documentation:
To the extent possible under law, the author(s) have dedicated all copyrightand related and neighboring rights to this software to the public domainworldwide. This software is distributed without any warranty.
You should have received a copy of the CC0 Public Domain Dedication alongwith this software. If not, seehttps://creativecommons.org/publicdomain/zero/1.0/.
The following people have helped with development or contributed their changesto the project and the public domain according to the Creative Commons PublicDomain Dedication 1.0 Universal:
Alexandr Sokolovskiy
See also
hmacA module to generate message authentication codes using hashes.
base64Another way to encode binary hashes for non-binary environments.
Generate 256 Bit Key Python Code
Official BLAKE2 website.
Generate 256 Bit Key Python Free
The FIPS 180-2 publication on Secure Hash Algorithms.
Wikipedia article with information on which algorithms have known issues andwhat that means regarding their use.
Python Generate 256 Bit Key
PKCS #5: Password-Based Cryptography Specification Version 2.0